Prioritizing Data Center Security
It takes a whole host of resources and know-how to address the complexities of data center security. Preventing attacks and securing operations require a substantial budget to keep pace with existing and future challenges. A report from Markets and Markets predicts that data center security spending will reach $13.77 billion next year. More than 34% of CIO.com’s 2020 State of the CIO respondents agree, indicating security and risk management is already “the number one driver of IT spending.”
Increased spending indicates the need for ongoing protection against cyberattacks. In 2019, research conducted by the Ponemon Institute reported that the average breach cost $3.92 million. Reducing security threats, outages and downtime mean profits and reputations are saved.
Companies must be prepared to invest in the people, processes and technology to protect data centers from security breaches.
Read on to learn more about:
- Fundamentals of security for on-premise and cloud data centers
- On-premises vs. cloud security comparison
- Data center security requirements and standards/best practices
- How to implement data center defense
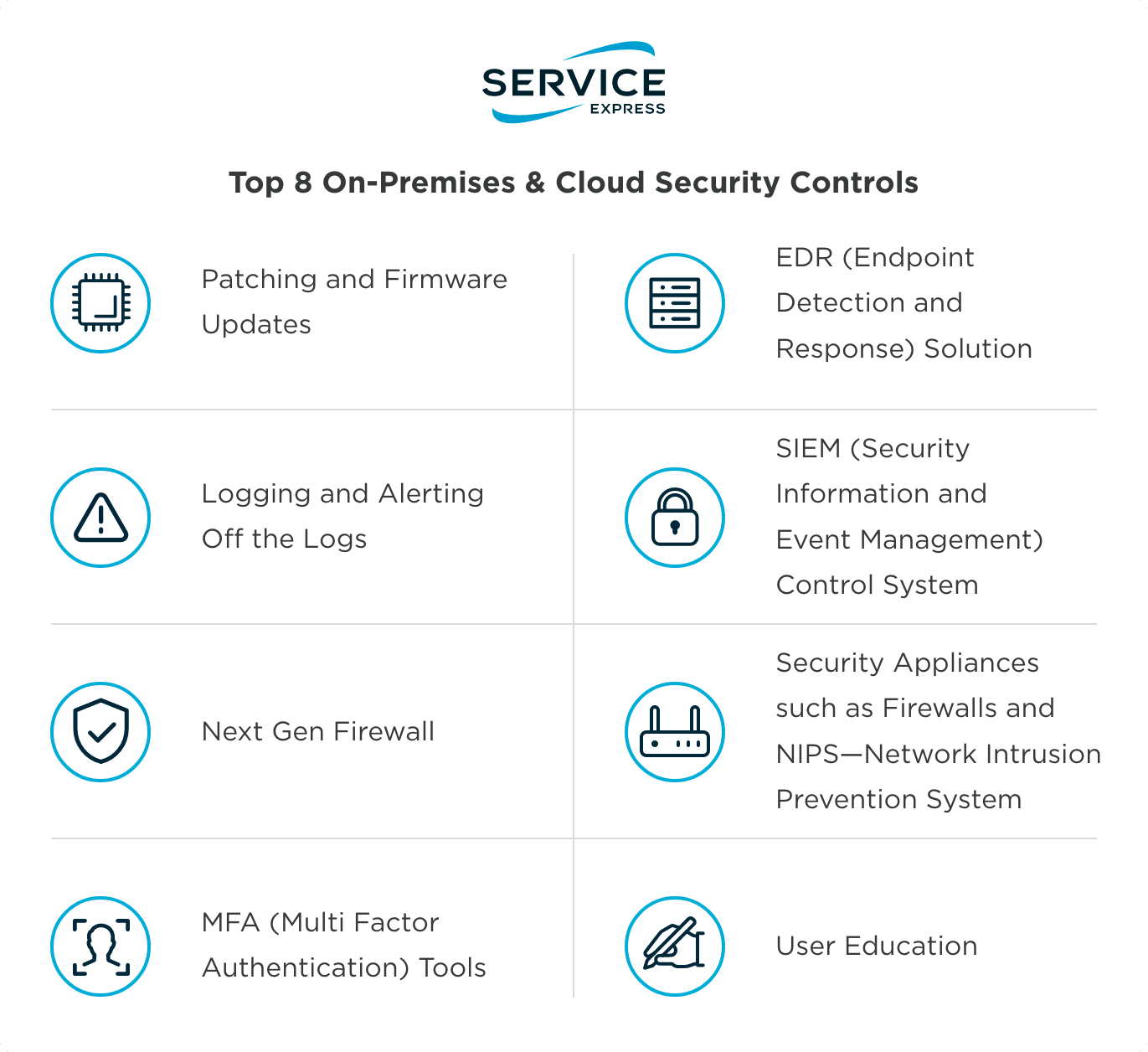
- Top 8 on-premises & cloud security controls
- What does the future of data center security hold?
Compare & Contrast: On-Premises vs. Cloud Service Security
The on-prem versus cloud security debate continues within the data center industry. The differences range from minor to substantial, but both on-prem and cloud advocates can agree that countless protections and threats exist in either environment. Beyond focusing solely on meeting IT security priorities, the question is: which is more secure for my organization and its business objectives?
On-Prem Security
PROS
Increased Control
More control over security is retained when a company manages services with its own on-prem servers.
Infinite Customization
On-Premises serves to allow network customization that is tailor-made for a company’s needs.
More Reliable
On-prem servers do not rely on an internet connection.
Quicker Learning Curve
The majority of IT professionals are better equipped to build security processes in this environment.
Lower Total Cost Of Ownership (TCO)
On-prem servers may require a larger upfront investment in hardware and installation, but in the long run, security is less expensive to maintain with a third-party support strategy.
CONS
Timely To Scale
Procurement of IT hardware can take time and research to scale security for on-prem data centers.
Increases The Need For On-Site Security
Without the right team and safety controls in place, some businesses may be more vulnerable to physical threats such as damage to physical property.
Security In The Cloud
PROS
Easier To Scale
Expanding storage for data in the cloud is as straightforward as upgrading a cloud storage package.
Faster Set-Up
Cloud-based security is more automated, which means set-up takes minutes rather than days.
Flexible Pricing Structure
Cloud computing often has a more flexible pricing structure with “pay-as-you-grow” fees.
CONS
Increased Vulnerabilities
The cloud’s larger attack surface can make it particularly vulnerable to cyberattacks.
Limited Control
An issue with one cloud-based data center customer could compromise another customer’s data.
Limited Customization
Traditional monitoring and security tools do not always work in cloud environments.
Regulation Issues
Some regulations require that the shared responsibility of multi-tenant hardware is not used.
More Expensive
Cloud computing often has a more flexible pricing structure with “pay-as-you-grow” fees, but is less predictable for forecasting unforeseen costs and is more expensive in the long term.
“The biggest challenge to data center security today is not physical threats but rather cyber threats. The proliferation of applications and burgeoning mounds of intellectual property and private information often governed by regulators — make data centers a central target for cybercriminals and even nation-states…the cyberattack surface for the data center is expanding and becoming increasingly harder to defend.
These threats can target physical devices and systems used to manage cooling and video surveillance, among others. They can also target personnel through spear phishing, gaps in authentication protocols, and other malicious means.”
– Digital Reality
Data Center Security Requirements & Standards
Requirements should be reviewed to understand how they will ensure and impact data center safety. Many industries demand unique security standards, involving a formal third-party auditing process to demonstrate compliance. Though complying with standards and requirements with all their details and steps appears daunting, these established best practices do shape a security response that can protect you from potential harm, downtime and data loss.
Industry security standards include:
- NIST 800-88 Guidelines for Media Sanitization
- HIPAA in healthcare
- FERPA in educational institutions
- PCI DSS for credit cards
- ISAE 3402 for data center financial reporting
- ISO 27001 Information Security Management System
- Standard—most widely-accepted certification for supporting information security, physical security, and business continuity
Regardless of industry, IT professionals should, at a minimum, be familiar with data center tiers and the kill chain standards. Uptime Institute’s Tier Classification System serves as a benchmark for ensuring maximum uptime. Lockheed Martin’s six-step Cyber Kill Chain® helps align defense strategies against cybercriminals.
Implementing Data Center Defense
To protect data centers from new and expanding threats, IT leaders should layer security defenses for overlapping on-premises and cloud-based environments. Layering is a relatively simple concept. The idea is that all individuals should be forced to breach several layers of security before they reach data. In doing so, the “Zero Trust” framework is upheld: everyone is subject to the same high level of scrutiny.
Top Priority: Strengthening Security & Privacy
According to our 2021 Data Center & Infrastructure Report, 48% of respondents identified strengthening security and privacy as a top priority.
What Does the Future of Data Center Security Look Like?
Cloud technology is trending now, but factors such as rising costs and security vulnerabilities are impacting its adoption. With more experience and a better understanding of the pros and cons, IT leaders are looking to a hybrid model for bringing together the scalability of the cloud with the control of on-premises data centers.
Topics:




